Mac Spoofing Kali

The first step in spoofing your MAC address is to find the network interface device that you want to spoof. Go to StartControl PanelNetwork Connection. Then double click on the device that you want to spoof. Then click on the support tab and then click on details. Then in the list you will see the MAC address. Step 2: Spoof the Mac Address.
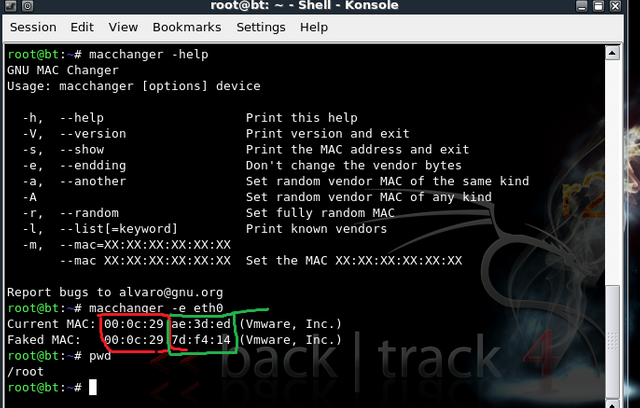
There are many reasons for spoofing a MAC Address and its very easy as limited to few commands.
To spoof MAC Address on Kali linux you will first make set your interface so for this type
now monitor interface is set to mon0 but to spoof we have to down wlan0 for a while so type
now wlan0 is down and now we will spoof the mac address by typing one simple command which is below and replace the mac address with MAC in the command i.e in my case the client has F0:CB:A1:2A:FB:62 so i will type ” ifconfig wlan0 he ether F0:CB:A1:2A:FB:62
Once you have did this you will have to turn the wlan0 so for this purpose type
Download and Install Panopto Recorder (Mac) The Panopto Recorder application allows you to easily create content. Once installed, it can be launched from your desktop or from your browser at ub.hosted.panopto.com. Applies To: UB faculty and staff. Student recording is limited to Assignments Folder only. Panopto support. Panopto for Mac Installation. Download Panopto for Mac by logging-in to your Panopto site and selecting Download Recorder located at the top right hand corner of the webpage (Fig. Figure 1 1.2. Run the 'Panopto.pkg' file. Click Continue (Fig.
After that you’re done and your Mac Address is been completely Spoofed
Jason, CEO/Lead Engineer JNETechnologies. FMR--USAF Special Operations Command at A.F. Information Warfare Center FL, NV. Simply put, I assign a =<0.0 value to any 'Trace' objectives. If attempting to spoof BIG BROTHER, know this value. Mac ID Properties Emulation and Manipulation (MIPEN), my pen, abilities would NEVER exist if we did not conceive it. Further, I heard a story, from a guy, went like this: Iraq was enriching an element via centrifugal methods. There was a software CDD. This PCUI directly accessed and modulated a DCM which had had it's and 3217 of it's partner's MAC ID modified. Guess what? Found first round. Then deployit.exe. I can untangle ANY EMI's at will with a single (GOV) snap-in.FYI